Amazon’s AWS (Amazon Web Services) undergoing a huge maintenance in its US East 1 Region Data centers in North Virginia that created some buzz on the internet to down today. The websites including Quora, Time Inc, Flippa, Soundcloud, Adobe Services, Citrix, IFTTT, iFixit, Flipboard, Fiverr, MailChimp, Medium, Twilio, Signal and many other websites are already down and some websites were slow on 28th February.
Some other websites and mobile applications Airbnb, Pinterest, Freshdesk and many others which use AWS services are down for some hours. People from almost all part of the world facing major website down issues today. Many people thought it was an error from iOS and other cloud devices and reported them. But it was not from them, but from their servers which are hosted on AWS service.
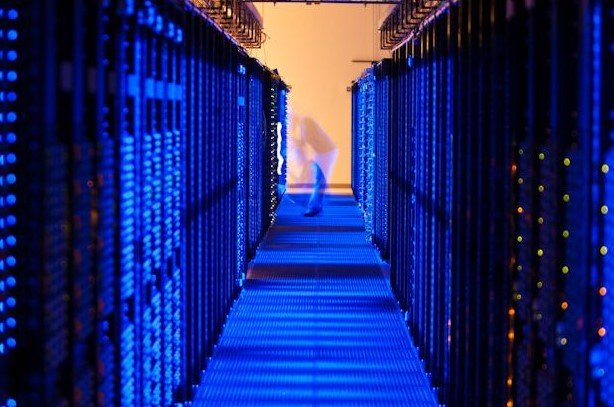
AWS Servers Down
If you are one among them, you no need to panic and report them, it is just a temporary maintenance issue from the AWS team. Here is an official twitter update from AWS team regarding the maintenance of the server.
The dashboard not changing color is related to S3 issue. See the banner at the top of the dashboard for updates.
— Amazon Web Services (@awscloud) February 28, 2017
UPDATE: AWS Server issues are fixed and all the websites which are hosted and using S3 are up now (28th Feb).
Checkout: ยูฟ่าเบท



